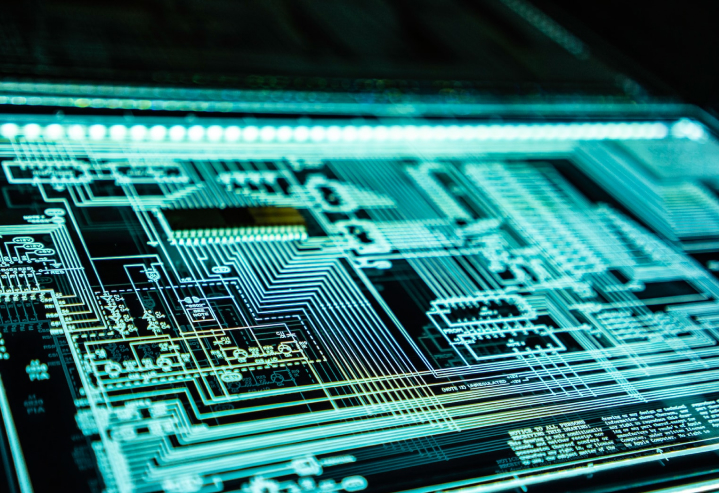
Cybersecurity Services for Businesses in Singapore
Strengthen Your Business with Cybersecurity Solutions



Cybersecurity Services




Tailored Cybersecurity Solutions for Singapore and ASEAN Businesses
Our Cybersecurity Solutions Portfolio

Cyber Incident Response Retainer

Cybersecurity Consulting
Email Phishing

JumpStart Managed Security Package
Managed Email Phishing

Vulnerability Management

Why Choose Our Cybersecurity Services
- We can become your trusted compliance and risk program consultant
- We deliver cost-effective technology and service to reduce enterprise-wide risk
- We identify & react to threats on your behalf
- Our team of experts can provide consulting services to support your in-house IT teams
- We can protect your applications & infrastructure by building state of the art systems powered by AI
Why Choose Our Cybersecurity Services
- We can become your trusted compliance and risk program consultant
- We deliver cost-effective technology and service to reduce enterprise-wide risk
- We identify & react to threats on your behalf
- Our team of experts can provide consulting services to support your in-house IT teams
- We can protect your applications & infrastructure by building state of the art systems powered by AI
Comprehensive Cybersecurity Solutions for Business Protection
- Identity Protection
- Endpoint Protection
- SIEM
- Network Protection
- Data Protection
Identity Protection
Endpoint Protection

Security Information and Event Management (SIEM)
Network Protection

Data Protection
Counter the prevalent cyber threats through an approach that prioritises identity security. Focusing on identities can bolster your holistic security strategy while diminishing the vulnerabilities tied to credential-related assaults. This approach is integral to adopting a Zero Trust network framework and other resilient cybersecurity solutions.
MyRepublic’s suite of identity and access management solutions streamlines access control and user account oversight. It fortifies safeguarding privileged credentials, supervises and concludes high-privilege user sessions, enforces multifactor authentication (MFA) and single sign-on (SSO) for warding off credential-driven attacks, and offers additional protective measures.As part of cybersecurity solution deployment, empower your Security Operations Center (SOC) with the capacity to oversee, supervise, and fortify a diverse array of endpoints and devices. Endpoints can expose your organisation to a plethora of threats if not adequately patched.
MyRepublic’s range of endpoint security offerings is designed to identify and remedy critical vulnerabilities, mandate passcodes or screen locks on all devices (whether Windows, iOS, or Android), introduce containerisation measures to uphold the security of corporate data, enable remote monitoring, locking, and device wiping, all while maintaining the seamless user experience and productivity.Enhance your Security Operations Center (SOC) with a pre-emptive security stance and equip them with comprehensive insight into your network events. SIEM solutions aggregate and assess logs from diverse sources, encompassing endpoints, firewalls, Active Directory, and more. These logs are then interconnected and evaluated in real-time to identify security breaches.
MyRepublic’s SIEM offering fuses threat intelligence with machine-learning-driven user behaviour analysis, alongside rule-based identification of potential attacks. This synergy aligns with the capabilities of cybersecurity solutions, proactively combating internal threats, safeguarding against data leaks, and averting compromising of user accounts. It streamlines incident response through automation and prevents malware attacks, further ensuring adherence to data privacy and security protocols such as PCI DSS, SOX, HIPAA, and GDPR.Networks stand as the vital framework of your organisation’s IT infrastructure. Safeguarding against network disruptions through cybersecurity solutions and guaranteeing rapid recuperation should a network catastrophe occur is crucial. The deployment of network security tools is pivotal in sustaining the uptime and resilience of your network in the face of cyber perils.
MyRepublic’s suite of network security offerings equips your team to vigilantly oversee and manage an evolving web of users, devices, and applications. It facilitates automated network backups to fortify disaster readiness, scrutinises network traffic for the identification of unauthorised devices and security breaches, rectifies misconfigurations, and delivers a range of additional capabilities.Data holds immense value in today’s digital landscape, akin to precious gold. Thus, safeguarding it is paramount. Data security solutions stand as the cornerstone in ensuring the sanctity of your data—ranging from customer personally identifiable information (PII) and payment card data (PCI) to intellectual property and other confidential content—whether it’s at rest, in transit, or during utilisation.
MyRepublic’s data security solutions empower your Security Operations Center (SOC) with comprehensive oversight of data dispersed across your network. They possess the capacity to identify and secure files housing sensitive information, conduct real-time monitoring of critical files, folders, and shares, and enact safeguards against data leakage. Furthermore, they work in tandem with cybersecurity solutions to proactively spot ransomware attacks in real-time and employ automatic countermeasures to thwart their expansion to other endpoints.Start Your Cybersecurity Journey with MyRepublic Business
Looking for reliable cybersecurity services in Singapore?
Get in touch with us.
Frequently Asked Questions
1. What are cybersecurity solutions? What do they encompass, and why is it important?
2. What types of cyber threats do cybersecurity solutions protect against?
Cybersecurity consulting typically includes risk assessments, vulnerability management, security strategy development, compliance guidance, incident response planning, and recommendations to improve overall cybersecurity posture.