Investing in Security: Saving Costs with VAPT Services
Experiencing a data breach can have severe and long-lasting financial consequences. The costs associated with such incidents often go beyond immediate financial losses. Companies may face expenses related to investigation and remediation, legal actions and settlements, regulatory fines, and the implementation of enhanced security measures. Beyond the direct costs, there can be indirect financial impacts, such as damage to reputation and customer trust, which always results in decreased revenue and loss of business opportunities. Organisations must prioritise robust cybersecurity practices to mitigate the devastating financial effects of data breaches.
Costs of Cybersecurity Incidents in Asia Pacific
The Asia Pacific region is one of the most vulnerable to cyber-attacks, with high levels of malware activity and an increasing number of reported cybersecurity incidents.
According to IBM’s Cost of a Data Breach Report 2023, the average cost of a data breach in the ASEAN region was US$3.05 million. The report also finds that detection and escalation costs are now the costliest category of data breach expenses, indicating a shift towards longer and more complex breach investigations. As little as six years ago, lost business costs, which include activities that attempt to minimise the loss of customers, business disruption and revenue losses, represented the largest share of data breach costs, but detection and escalation costs have been steadily rising.
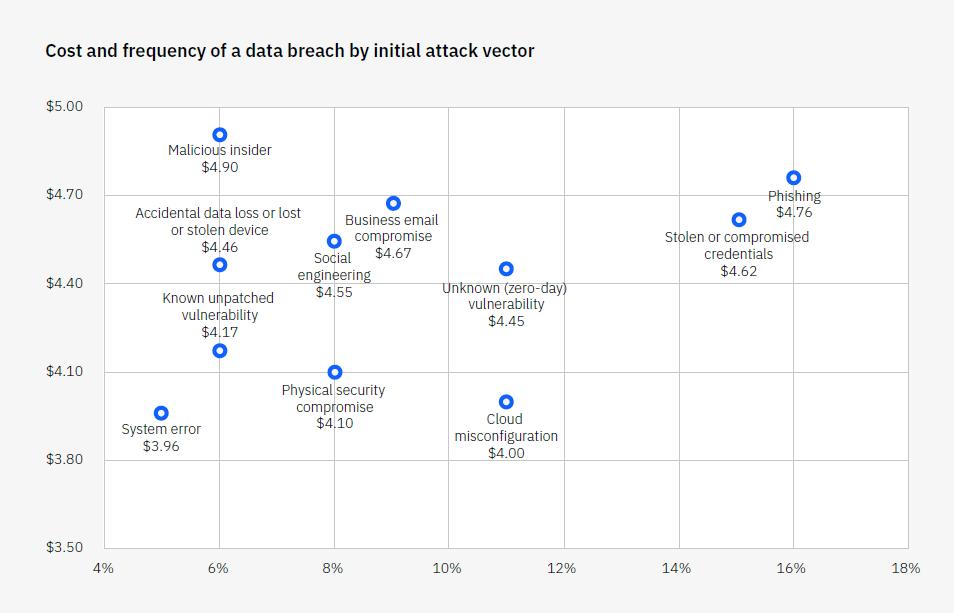
Caption: Cost and frequency of a data breach by initial attack vector (measured in USD millions)
Source: Cost of a Data Breach Report 2023 by IBM
In a global study of cybersecurity decision-makers, 80% of the respondents from Singapore said that security breaches in the past 12 months led to losses of up to 10% of their organisation’s revenue. Respondents from medium-size businesses estimated their company lost an average of 9% in revenue, while those from large enterprises said losses averaged 5% of revenue.
Understanding the True Cost of Data Breaches
The financial impact of data breaches extends far beyond the immediate costs of resolving the breach. Legal fees, compensation payouts, loss of business opportunities, reputational damage, and regulatory fines are just a few examples of the hidden expenses that organisations may face in the aftermath of a data breach.
Let’s explore some of the hidden expenses that organisations may face:
- Legal fees: When a data breach occurs, companies often need to seek legal advice and assistance. This can involve hiring lawyers to navigate through the complex legal landscape surrounding data protection and privacy. These legal fees can quickly add up and become a significant financial burden.
- Compensation payouts: In many cases, data breaches can lead to lawsuits from affected individuals seeking compensation for the loss or misuse of their personal information. Organisations may be required to pay settlements or damages to affected parties, which can be costly depending on the scale and severity of the breach.
- Loss of business opportunities: Data breaches can erode consumer trust and confidence in an organisation. This loss of trust can result in a decline in customer loyalty, reduced sales, and missed business opportunities. For example, if a company suffers a high-profile breach, potential clients or partners may be hesitant to do business with them, leading to missed partnerships or contracts.
- Reputational damage: The fallout from a data breach can have long-lasting effects on an organisation’s reputation. Negative publicity, media coverage, and public scrutiny can tarnish a company’s image and brand value. Rebuilding trust and restoring a damaged reputation can be a costly and time-consuming process.
- Regulatory fines and penalties: Depending on the jurisdiction and the nature of the breach, organisations may face regulatory fines and penalties for non-compliance with data protection laws. These fines can be substantial and can further contribute to the overall financial impact of the breach.
The IBM report divides the cost of data breaches into four categories – lost business, detection and escalation, notification and post breach response. Lost business costs include business disruption and revenue losses from system downtime, cost of lost customers and acquiring new customers, and reputation losses and diminished goodwill. Notification costs include activities that enable the company to notify data subjects, data protection regulators and other third parties.
Detection and escalation costs, which have been the costliest category of data breach expenses, include activities that enable a company to reasonably detect a breach, such as forensic and investigative activities, assessment and audit services, crisis management, and communications to executives and boards.
Post-breach response costs include activities such as legal counsel and services, credit monitoring for affected customers, identity theft protection, and public relations expenses.
Mitigating the Financial Impact of Data Breaches: Strategies and Best Practices
To minimise the financial impact of a data breach, organisations should focus on implementing strong security measures and robust incident response plans. This can include conducting regular risk assessments to identify potential vulnerabilities, implementing data encryption techniques, and providing employee training on cyber security best practices. Organisations should also have an incident response plan in place that outlines specific steps to take in the event of a breach, such as notifying appropriate parties and containing the breach to prevent further damage.
We’ve made a note of a few approaches to keep in mind:
AI & automation: As data breaches become more complex and costly, organisations are turning to artificial intelligence (AI) and automation to help detect and respond to breaches more efficiently. AI tools can analyse large amounts of data in real-time, helping to identify potential threats and vulnerabilities that may have otherwise gone unnoticed. Automation can also streamline incident response processes, reducing the time and resources needed for manual tasks.
Incident response teams can benefit from incorporating AI and automation into their processes – it would allow them to respond to breaches in a more timely and effective manner. This would help mitigate the financial impact of a data breach.
Data breach insurance: In addition to implementing preventative measures, organisations can also mitigate the financial impact of a data breach by obtaining data breach insurance. This type of insurance covers the costs associated with responding to and recovering from a data breach, such as legal fees, notification costs, and credit monitoring for affected individuals. Having data breach insurance can provide organisations with peace of mind and financial protection in the event of a breach.
Employee training: While technology and processes play a critical role in mitigating the financial impact of a data breach, it’s also important to educate employees on proper security protocols. Human error is one of the leading causes of data breaches, so training employees on how to recognise and prevent potential security threats can significantly reduce the risk of a breach occurring. This can include teaching employees about password hygiene, phishing scams, and other common tactics used by hackers.
Vulnerability and risk management: As technology continues to evolve, so do the tactics and techniques used by cybercriminals. It’s crucial for organisations to regularly assess their systems for vulnerabilities and prioritise risk management efforts accordingly. This can involve conducting regular security audits, implementing patches and updates, and staying informed about known vulnerabilities in software and hardware. Proactively addressing potential weaknesses helps organisations minimise the likelihood of a data breach occurring.
Managed security service providers (MSSPs): For organisations lacking the resources or expertise to implement comprehensive security measures, enlisting the help of a managed security service provider (MSSP) can be a valuable solution. MSSPs specialise in managing and monitoring IT security for their clients, providing round-the-clock protection against potential threats. This can include services such as intrusion detection, vulnerability scanning, and incident response planning. Organisations could outsource security to an experienced provider so that they can focus on their core business while maintaining a strong defence against cyber attacks.
How do VAPT services help reduce the cost of data breaches?
Proactive cybersecurity measures such as Vulnerability Assessment and Penetration Testing (VAPT) can drive substantial cost savings. Identifying and addressing vulnerabilities before they are exploited will help organisations prevent potential breaches and the associated financial damages. Moreover, proactive cybersecurity measures can also save costs by reducing downtime and maintaining business continuity. Organisations can prevent disruptions in their operations, avoid potential legal and regulatory penalties, and safeguard their reputation.
VAPT services can help organisations streamline their security efforts, allowing them to allocate resources and budget more effectively. With a comprehensive understanding of potential risks and vulnerabilities, organisations can prioritise their risk management efforts and make informed decisions about where to invest in security measures. This targeted approach can result in cost savings by avoiding unnecessary or ineffective security investments. This investment in VAPT services can ultimately save organisations money by preventing and mitigating the potential financial impacts of cyber attacks.
Further, some MSSPs offer VAPT services as part of their overall security management package, providing organisations with a comprehensive solution to their security needs while also reducing costs. Organisations can leverage the expertise and resources of an MSSP to benefit from cost-effective VAPT services while also gaining access to additional security capabilities such as threat intelligence, 24/7 monitoring and response, and ongoing support. This comprehensive approach can help organisations stay ahead of cyber threats while minimising costs associated with managing security in-house.
Mitigating Legal and Regulatory Expenses
Organisations often need to adhere to a wide range of laws, regulations, and standards when handling personal information. Compliance with data protection regulations is crucial to avoid penalties and fines. For instance, the General Data Protection Regulation (GDPR) in Europe requires businesses to protect the personal data of EU citizens or face significant financial consequences. Failure to comply with GDPR can result in fines of up to 4% of annual global turnover or €20 million, whichever is higher.
The Health Insurance Portability and Accountability Act (HIPAA) in the United States sets standards for protecting individuals’ medical information. Non-compliance with HIPAA can lead to severe penalties, including substantial fines and even criminal charges.
Organisations that do not have the necessary expertise and resources to ensure compliance with these regulations can turn to VAPT services for assistance. VAPT service providers can guide regulatory requirements, help implement appropriate controls, and conduct regular assessments to ensure continued compliance.
VAPT services help identify vulnerabilities in data systems and networks, allowing organisations to address them proactively. Businesses can use VAPT assessments to stay ahead of potential security risks and maintain compliance with data protection regulations. This would help them effectively mitigate legal and regulatory expenses while safeguarding sensitive data.
VAPT for Long-Term Financial Resilience
It is clear how services like VAPT have an important role in building a financially resilient business. Preventing data breaches helps businesses avoid substantial financial losses and secure their financial future. Investing in VAPT allows businesses to demonstrate their commitment to security and trustworthiness and helps them stay ahead of the competition.
Businesses need to remember that the costs associated with VAPT are an investment. Investing in regular penetration tests can help identify potential vulnerabilities before they are exploited and save companies from costly remediation efforts down the road. Companies that invest in VAPT now can enjoy the long-term financial rewards of data security and trustworthiness.
At the end of the day, businesses are responsible for their financial security and should take all necessary measures to protect it.
Conclusion
VAPT represents a powerful tool for businesses and should be included as an integral part of any comprehensive cybersecurity strategy. As technology advances, companies must remain vigilant in protecting their data and assets to ensure the long-term financial security of their business.
Data breaches can have crippling financial consequences for businesses. Proactively using VAPT services will help businesses avoid the costly aftermath of breaches and ensure their long-term financial stability and success.
Investing in this technology is essential for companies wishing to maintain data security and trustworthiness in an increasingly complex digital landscape. As such, it should be considered a key part of any business strategy for secure and successful financial operations.